The journey towards digital transformation in India has reshaped numerous governmental processes, with driving licence verification emerging as a key area of innovation. Traditionally, this process was laden with paperwork and physical visits to transport offices, often leading to inefficiencies and delays. The introduction of online verification represents a significant leap towards modernisation, aligning with initiatives like Digital India aimed at simplifying citizen-government interactions.
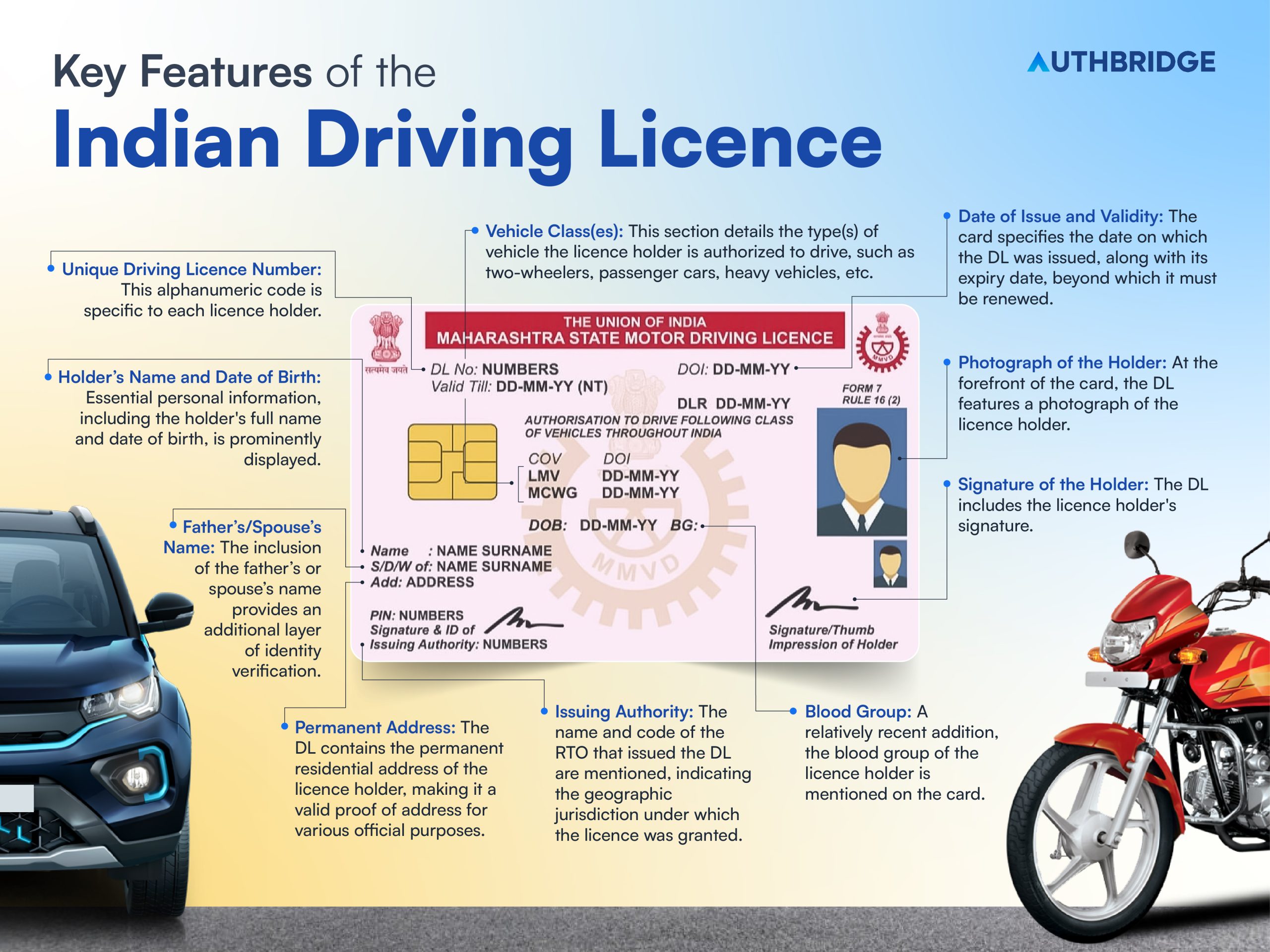
Let’s delve into the key features and details contained within an Indian driving licence:
- Photograph of the Holder: At the forefront of the card, the DL features a photograph of the licence holder, serving as a crucial identification mark.
- Unique Driving Licence Number: This alphanumeric code is specific to each licence holder, facilitating easy tracking and verification of the individual’s driving credentials.
- Holder’s Name and Date of Birth: Essential personal information, including the holder’s full name and date of birth, is prominently displayed, further aiding in identification.
- Father’s/Spouse’s Name: The inclusion of the father’s or spouse’s name provides an additional layer of identity verification.
- Blood Group: A relatively recent addition, the blood group of the licence holder is mentioned on the card, which could be critical in emergency situations.
- Permanent Address: The DL contains the permanent residential address of the licence holder, making it a valid proof of address for various official purposes.
- Issuing Authority: The name and code of the RTO that issued the DL are mentioned, indicating the geographic jurisdiction under which the licence was granted.
- Date of Issue and Validity: The card specifies the date on which the DL was issued, along with its expiry date, beyond which it must be renewed.
- Vehicle Class(es): This section details the type(s) of vehicle the licence holder is authorized to drive, such as two-wheelers, passenger cars, heavy vehicles, etc.
- QR Code: Modern DLs come with a QR code that, when scanned, directs to a digital verification page showing the licence’s authenticity and other details. This feature significantly enhances the security and ease of verification.
- Signature of the Holder: The DL includes the licence holder’s signature, providing an additional authentication method.
Online DL verification has become a milestone in increasing the safety, reliability, and integrity of driver verification processes. It not only streamlines administrative operations but also elevates the level of access and convenience for the masses. This digital shift is pivotal in combating fraud, ensuring only qualified individuals are behind the wheel, thereby contributing to road safety and regulatory compliance.
In the rapidly digitising landscape of India, online driving licence verification has emerged as a critical tool across various industries. This process not only enhances operational efficiencies but also plays a pivotal role in ensuring safety, compliance, and authenticity. Let’s explore the significance of online DL verification across different sectors in India:
Transportation And Logistics
In the transportation and logistics sector, the verification of driving licences is extremely important. It ensures that only qualified individuals operate vehicles, thereby reducing the risk of accidents and ensuring compliance with road safety regulations. For businesses, this verification process aids in building a reputable brand that prioritises safety and reliability. Moreover, it streamlines the hiring process, enabling quicker validation of a candidate’s credentials, significantly reducing the administrative burden and expediting the onboarding of new drivers.
Car Rentals And Ride-Sharing Services
For car rental and ride-sharing companies, trust is a currency. Online DL verification ensures that drivers have valid licences, which is crucial for customer safety and trust. It also serves as a risk management tool, reducing the likelihood of incidents that could lead to legal liabilities. By leveraging digital verification, these companies can quickly onboard new drivers, ensuring they meet the safety standards required to provide a secure service to customers.
Financial Services And Insurance
In financial services and insurance, DL verification plays a critical role in fraud prevention and risk assessment. Insurance companies can use DL verification to prevent fraudulent claims by ensuring the policyholder’s driving licence is valid at the claim. Similarly, financial institutions offering vehicle loans can assess the risk profile of applicants based on their driving records, leading to more informed lending decisions.
Employment Background Checks
For roles that require driving as a primary duty, employers leverage online DL verification to validate the authenticity of the credentials provided by applicants. This not only ensures compliance with regulatory standards but also safeguards the organisation against potential liabilities arising from accidents involving unqualified drivers. Digital verification processes enable employers to conduct these checks efficiently, saving time and resources in the hiring process.
Hospitality And Tourism
In the hospitality and tourism industry, where employees often transport guests, verifying the driving licences of employees is essential for maintaining safety standards. It also protects the company’s reputation by ensuring that guests are in safe hands. Digital verification allows for quick checks, ensuring that all drivers meet the necessary legal requirements to operate a vehicle, thereby enhancing guest safety and satisfaction.