Businesses rely on numerous third parties for the smooth running of key operations, increase profitability, and go to market faster. Third-party stakeholders such as suppliers, vendors, dealers, distributors, vendors, and merchants play an integral part in managing different functions of the supply chain. With the help of third parties, businesses can overcome the complexity of supply chain functions, fill the gaps for smoother operations, and expand channels to customers.
Unfortunately, third-party vendor relationships come with unforeseen risks and vulnerabilities and can expose a business to reputational, regulatory, and financial risks. Establishing a robust technology for due diligence and continuous monitoring is essential to assess hidden risks at an earlier stage and mitigate them with various risk assessment techniques.
What is Third-Party Due Diligence?
Third-party due diligence often involves putting various levels of checks and balances within your new vendor, supplier, or any third-party onboarding journeys. This process usually involves onboarding contract review, vendor-completed assessments, and external intelligence. All of this is weighed against your organization’s level of risk tolerance.
A comprehensive due diligence process enables businesses to accelerate vendor onboarding while mitigating the possibility of any information insufficiency.
Types of third-party risks in supply chain networks and how to mitigate them?
We have identified five major types of supply chain risks along with the risk mitigation techniques.
Informational Risks
a. What are informational risks?
When onboarding vendors and third parties, it is crucial to collect relevant information and documents for identity validation and ensure all the information provided is correct in the first place. Most third parties have access to privileged and highly confidential data, such as financials, customer information, or intellectual property. In case there are un-vetted third parties in the system, there are high chances of a data breach as they have access to sensitive information or systems.
b. How to mitigate them?
Conducting due diligence of third parties with AI-backed technologies like biometric identification, image recognition, and liveness detection makes much more sense to validate individuals in real-time and mitigate informational risks. Businesses can validate ID documents with no hassles via OCR ensuring automated form filling and converting physical documents into digital. Some of the top key checks i.e. KYC/KYB checks, document validation, business ID verification, national ID verification, and much more help prevent informational risks, validate third parties, and identify stolen IDs, and forged documents.
Operational Risks
a.What are operational risks?
The rise of third-party relationships has increased operational risks across various functions, delivery channels, and processes as businesses don’t have the direct control and visibility of the third-parties activities. Operational risk is the risk of loss resulting from inadequate or failed internal processes, people, or systems. Cumbersome verification processes delay the onboarding of third parties and create difficulties for the businesses to perform their daily operations. Sometimes third parties are unable to serve what they promised earlier, creating troubles in the smooth business functioning. Thus, it is mandatory to have a robust due diligence solution in place to ensure real-time verification, seamless onboarding, and continuous monitoring to eliminate the scope of operational risks.
b.How to mitigate them?
Our digital address verification combines image recognition, GEO-tagging coordinates, and liveness detection technologies to verify the identity and physical address from their smartphones and enable identity verification in real-time. Continuous risk monitoring can empower businesses with the right security metrics and identify third-party risks before they become problematic. This also helps streamline remediation efforts and take a decisive call specific to each third party.
Financial Risks
a.What are financial risks?
Any misconduct by unvetted third parties not only hampers the reputation but also incurs financial charges or penalties – impacting your business standing in the marketplace. Some of the top financial risks are Market Risk, Credit Risk, Operational Risk, and Legal Risk. It is crucial to evaluate whether an individual/business partner is a good prospect or in any financial trouble.
b.How to mitigate them?
Businesses can mitigate financial risks with Know Your Customer/Know Your Business (KYC/KYB) checks, Anti-money laundering checks, high-risk EDD, ongoing monitoring, PEP checks (Politically Exposed Persons), risk scoring, and criminal watchlist checks. Conduct financial checks to determine bank account authenticity, GST number verification, financial standing, or any active mortgage/satisfied charges.
Reputational Risk
a.What are reputational risks?
Reputational risk is related to the image/perception of your company in the marketplace. Any misconduct by a third party can put the reputation of your business in dire straits. Reputational risks also occur when businesses have an association with a third party who has a history of violating rules and regulations or data breaching of sensitive information.
b. How to mitigate them?
Businesses must conduct reference checks to get a detailed report of financial stability, reputation aspect, linked associations, any sanctions/criminal history and stay protected from reputational risks. They must leverage insight-driven business intelligence platforms to enable risk assessment and choose genuine third parties, and business partners. With the help of customizable workflows, easy plug-and-play APIs, and comprehensive reporting, businesses can streamline the entire due diligence process and conduct risk analysis in just a few clicks.
Regulatory Risks
a. What are regulatory risks?
Regulatory risks arise due to a change in laws and regulations that could potentially cause business loss or violations of existing ones. These risks often result from insufficient control systems, lack of due diligence, and human error. Such risks can expose your business to various damages such as legal penalties, voided contracts, loss of opportunities, and reputation.
b. How to mitigate them?
Some acts and regulations must be taken into consideration for the due diligence of third parties. The rules and regulations differ from industry to industry. Some that span across industries are IT ACT 2000, FCPA, FDA, FASSI, and EIDAS. Businesses must prioritize third-party due diligence considering these regulations to safeguard themselves from regulatory and illegal financial problems.
Isn’t it surprising that your business is prone to risks at various levels? Wondering what are the top checks to mitigate third-party risks?
How are AuthBridge’s third-party due diligence solutions helping various industries?
Know Your Customer
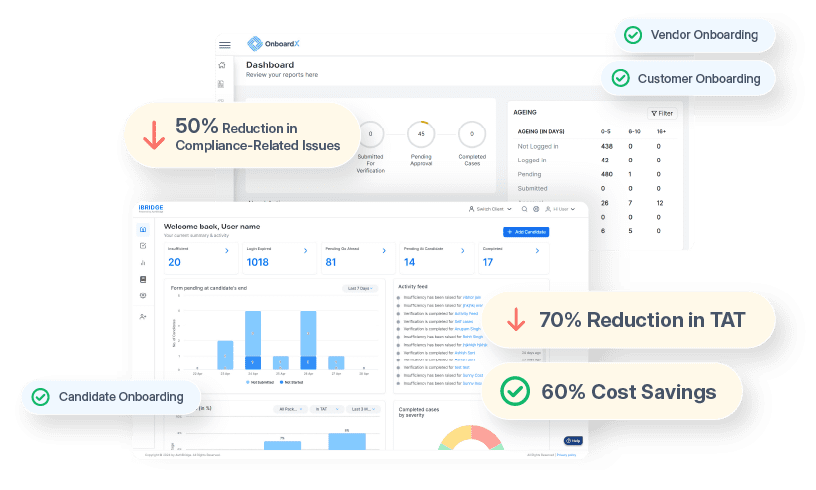
We have optimized various B2C, B2B, and B2B2C onboarding processes for our wide range of clients across 30 industries with the help of our platform – OnboardX. We have successfully mitigated the informational, reputational, and regulatory risks with our 117+ checks and proprietary databases.
Know Your Risk
We worked closely with our clients to reduce risk exposure and improve their high-risk processes. Our solutions like TruthScreen and CorpVeda have helped our clients manage end-to-end risk assessment and meet compliance with all regulations.
We continuously strive for excellence with customer satisfaction. Our unwavering attitude, efficient solution stack, and dedicated team of solution experts have helped our customers solve problems that were considered unsolvable.
We would be happy to answer all your questions and serve you the best. Please feel free to book a brainstorming session with our team of experts.